Your individual data may be moved from 1 processor to one more. You require to recognize exactly how they're processing individual information which Helpful hints they're doing so with the consent as well as in maintaining with the GDPR. It's feasible to also begin to uncouple information. When data is collected, the organization needs to ensure it's kept in a secure fashion as well as in conformity with the Safety and security regards to the GDPR. As time passes, the complete amount of customer data expands considerably.
Going onward, yet the processor has as much of a passion in making sure responsibilities are precisely defined due to the fact that it'll be until now much more exposed. Cpus may also choose to designate a DPO even in situation they do not fall under one of the defined groups, or they could have to do so under Member State law. To the contrary, as long as the processor is entailed, you aren't totally free as a controller. Cpus are required to refine personal data because the controller's guidelines. Cpus, like controllers, are anticipated to carry out ideal safety procedures.
People are currently in a position to ask companies at any type of chance to remedy or update their data if the details is no longer exact. When an organization can not verify the method by which they have acquired approval the probability is they will be fined. It may only have a single 23-year-old or a single male in an office.
![]()
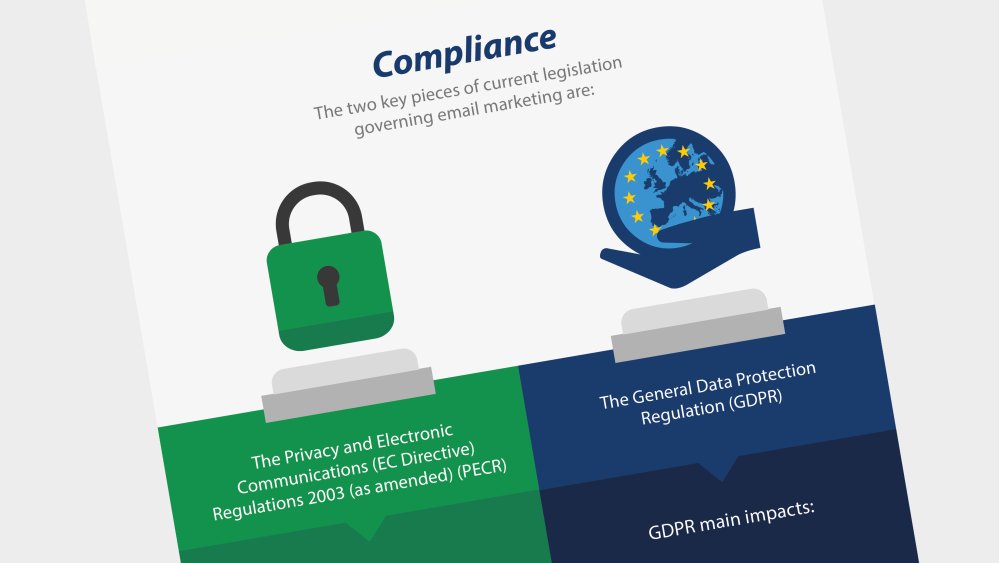
An effect assessment should concentrate on the following factors. Hence, a case-by-case assessment is critical. Another fantastic reason behind an audit is to determine as well as handle the dangers to stop information violations. You need to be able to demonstrate conformity. The demand that the data subject be found within the Union needs to be assessed currently as quickly as the appropriate trigger task occurs, i.e. at the here and now time of an offering of product and services or the moment as quickly as the behavior is being kept track of, regardless of the size of the deal made or the tracking that's carried out. There are 2 important parts of the Regulation that we would certainly like to highlight. If you're taking the vital actions to comprehend and also stick to the GDPR laws and also take part in good e-mail advertising and marketing ideal methods, you get on the suitable path to securing on your own.
The data controller (the site) ought to offer the individual with information to make sure that the individual can develop a decision on an enlightened basis. For auditors to fill out the endeavor of the potency of IT regulates on data handling, a skilled program was https://en.wikipedia.org/wiki/?search=DPIA produced.
When you possess an internet site, you're the information controller. When a site would like to process exclusive info concerning a kid it need to consider whether the kid is furnished to offer permission by itself or whether the authorization requires to be acquired by means of a parent (or guardian). Is info not adequately offered on exactly how finest to withdraw authorization, it is not http://www.bbc.co.uk/search?q=DPIA concerned as valid consent.

Consent shouldn't be considered freely provided in situation the information subject does not have any type of authentic or absolutely free alternative. Additionally, you need individual grant assemble name, email, and also telephone number on your site call kind. The authorization of the individual must be supplied in the shape of an unambiguous declaration.
In every one of the above instances, permission really isn't one of the most proper lawful structure for handling information. As mentioned by the GDPR, approvals need to be saved for five years. Rather, a various consent needs to be caught at the factor of acquisition that's certain to the intent of sending out advertising and marketing emails or sharing their information with companion companies. You likewise ought to make it easy for people to take out consent anytime, ideally in the precise fashion as they first consented. Quite just, approval has actually to be concretized in such a fashion that it's plainly stated what consent is provided to. When it is inadequate after that you have to discover the appropriate permission now.